
Protecting businesses since 2016 with our award winning AI Powered Cyber intelligence services
Menu

This service enables you to tailor your information security compliance approach by undergoing ISO 27001 and/or NIST security compliance checks.

We continuously monitor dark web, deep web and hacker groups, providing real-time insights into potential threats and vulnerabilities.
Invoke this service in the event of an actual or suspected cybercrime. Our team of expert investigators and forensic analysts trace and mitigate potential risks to you.
Obtain detailed reviews of partners and suppliers to determine risks originating from your supply chain.

With transparency unmatched by other cyber-risk evaluations, Darkscope helps brokers and underwriters understand the cyber security risks posed by organizations seeking cyber-risk insurance.

Darkscope’s Domain Monitoring Service is a comprehensive solution that continuously monitors your domain and associated assets for potential threats, unauthorized activities, and security vulnerabilities.
Offering flexibility in information security compliance, our service allows customers to tailor their approach by choosing between an ISO 27001 or NIST security compliance check.

For those prioritizing international standards, ISO 27001 establishes a robust framework, focusing on the establishment and continual improvement of an Information Security Management System (ISMS). On the other hand, customers opting for the National Institute of Standards and Technology (NIST) guidelines gain access to a comprehensive set of cybersecurity controls and risk management practices.
Whether aligning with ISO 27001 or NIST, our compliance checks ensure a thorough evaluation of your organization’s information security controls, policies, and procedures. This tailored approach enables you to address specific industry requirements or compliance preferences while reinforcing your commitment to effective cybersecurity practices.
Choose the compliance framework that aligns best with your organizational needs and industry standards, demonstrating a proactive stance against evolving cyber threats.
Joerg Buss, the visionary founder of DarkScope, has left an indelible mark on the world of cybersecurity through his significant contributions to the development of ISO 27001 standards. These standards, now universally recognized and adopted, serve as the cornerstone for information security management systems (ISMS) across various industries worldwide.
As advisors, leveraging Joerg’s foundational contributions to ISO 27001 allows us to offer our customers informed guidance rooted in industry best practices. By understanding the principles and intricacies of these standards, we can assist organizations in fortifying their cybersecurity posture and navigating the complex terrain of digital risk management with confidence and clarity.
Darkscope provides comprehensive dark web, deep web and hacker group monitoring services, offering businesses real-time insights into potential threats and vulnerabilities within the hidden corners of the internet to enhance cybersecurity.

DarkScope’s pioneering AI technology represents a paradigm shift in cybersecurity, transcending conventional boundaries to provide comprehensive monitoring and protection across the entire digital landscape. Unlike traditional solutions limited to monitoring the surface-level internet or specific dark web forums, DarkScope’s award-winning AI harnesses the power of machine learning and advanced algorithms to traverse the depths of the World Wide Web, including its deep and dark recesses.
By employing a sophisticated blend of data crawling, natural language processing, and anomaly detection, DarkScope’s AI continuously scans and analyzes vast swathes of online data in real-time. This proactive approach enables us to uncover emerging threats, identify malicious activities, and anticipate potential breaches across a spectrum of online environments.
DarkScope’s unique capability to monitor not just the dark web but the entire internet empowers organizations with unparalleled visibility and insights into their digital footprint. Whether it’s uncovering underground marketplaces, detecting data leaks, or mitigating brand reputation risks, our AI-driven platform provides a holistic view of cyber threats, allowing businesses to stay one step ahead of cyber adversaries.
Furthermore, DarkScope’s AI is constantly evolving, learning from new data patterns and emerging threats to enhance its predictive capabilities and adapt to evolving cyber landscapes. This dynamic intelligence ensures that our clients receive proactive and targeted security measures tailored to their specific needs, safeguarding their digital assets and preserving trust in an increasingly interconnected world.
12% of the webs content, where we can find risks other can’t.
The Deep Web hosts private hacker networks that we can penetrate.
In 2024 the majority of hacks are organized through social media.
Our expert investigators and forensic analysts are ready to respond swiftly to any suspected incidents, employing sophisticated techniques to trace and mitigate potential risks.
In the digital era, the specter of cyber fraud looms large over industries of all sizes and sectors. When faced with a cyber fraud crisis, timely and effective support becomes paramount for businesses to navigate the complex landscape of threats, mitigate damages, and restore trust among stakeholders.
First and foremost, industries must recognize that cyber fraud crises are not merely technological challenges; they are multifaceted crises that can have far-reaching repercussions across an organization. From financial losses and reputational damage to regulatory penalties and legal liabilities, the impacts of a cyber fraud incident can be profound and long-lasting. Therefore, industries need comprehensive support mechanisms that address not only the technical aspects of cyber fraud but also its broader operational, legal, and reputational implications.
One of the critical components of support during a cyber fraud crisis is access to specialized expertise and resources. This includes skilled incident response teams, forensic analysts, legal counsel, and crisis communications experts who can rapidly assess the situation, contain the breach, and coordinate an effective response. These professionals play a crucial role in identifying the root cause of the incident, preserving evidence for investigation, and implementing remediation measures to prevent further damage.
In the event of a suspected fraud or cybercrime, Darkscope’s fraud support services provide investigation and digital forensics expertise. This involves analyzing the details of the incident, gathering digital evidence, and tracing the source of the fraudulent activity to understand the methods used by perpetrators.
Darkscope conducts risk assessments to identify vulnerabilities within an organization’s systems and processes that could be exploited by fraudsters. By understanding potential risks, these services help implement preventive measures, such as enhanced security protocols, employee training, and system upgrades, to reduce the likelihood of future fraudulent incidents.
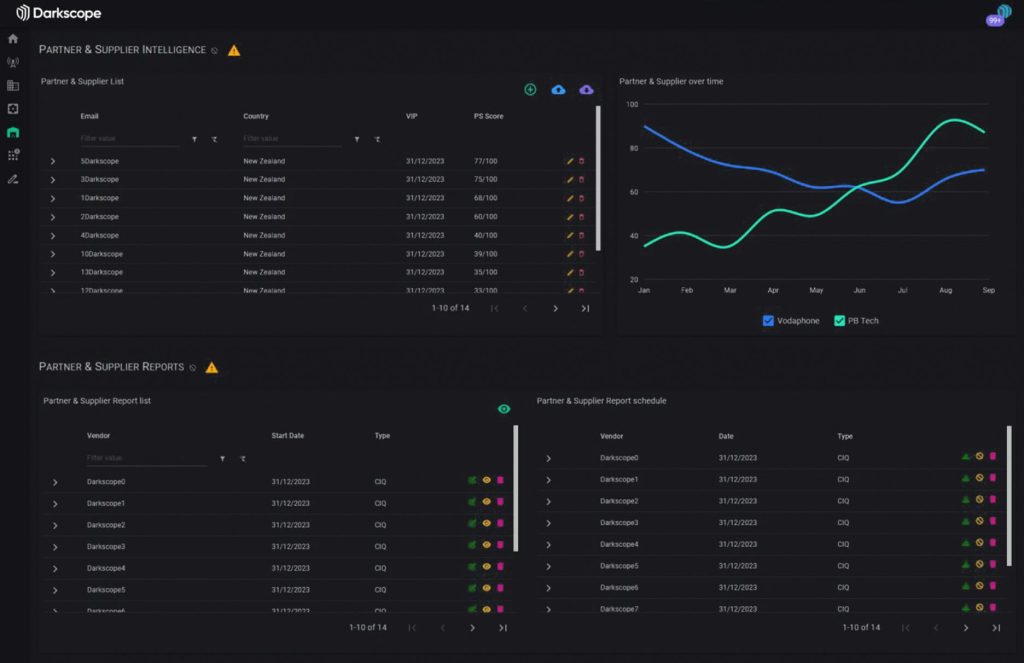
Darkscope’s Supply Chain Monitoring Service leverages advanced cyber intelligence techniques and cutting-edge technologies to provide comprehensive oversight of your entire supply chain network. Our service ensures continuous monitoring, risk assessment, and mitigation to protect against disruptions and vulnerabilities.

Real-Time Monitoring: Utilize real-time data analytics to monitor every stage of the supply chain, enabling immediate detection and response to potential issues.
Risk Assessment: Conduct thorough risk assessments to identify and address vulnerabilities within the supply chain, including cyber threats, and compliance issues.
Predictive Analytics: Employ predictive analytics to forecast potential disruptions and provide proactive solutions to maintain supply chain continuity.
Supplier Verification: Perform rigorous supplier verification to ensure that all partners adhere to industry standards and best practices, reducing the risk of fraud and non-compliance.
Incident Response: Implement robust incident response protocols to swiftly address and resolve any supply chain disruptions, minimizing downtime and financial impact.
Darkscope’s Domain Monitoring Service is a comprehensive solution that continuously monitors your domain and associated assets for potential threats, unauthorized activities, and security vulnerabilities. By utilizing advanced cyber intelligence and machine learning algorithms, our service provides real-time alerts and actionable insights to safeguard your online presence.

Continuous Monitoring: Perform 24/7 monitoring of your domain, including subdomains and related assets, to detect any suspicious activities or changes.
Threat Detection: Identify and alert on potential threats such as phishing attacks, malware, domain hijacking, and unauthorized access attempts.
Brand Protection: Monitor for unauthorized use of your brand, trademarks, and intellectual property across the internet, including dark web and social media.
Vulnerability Scanning: Conduct regular scans to identify security vulnerabilities within your domain infrastructure and provide recommendations for mitigation.
Incident Response: Offer immediate incident response support to address and neutralize threats, minimizing potential damage and downtime.
Detailed Reporting: Provide comprehensive reports and dashboards that offer insights into the security status of your domain, historical data, and trend analysis.
Customizable Alerts: Enable customizable alerts to notify you of critical issues based on your specific needs and risk tolerance.
A threat scan of your entire external attack surface can help provide you with peace of mind about your current security position and point you in the right direction to improve.

Darkscope’s Cyber Interference Risk Score profiles and rates the risks of a cyberattack for an organisation, not just their readiness or ability to respond. A Cyber Risk Score delivers more than a maturity based assessment can, as it looks beyond the walls of the organisation to the root of cyberthreats.
As an organisation builds their digital footprint; to increase market presence and competitiveness and make it easier to interact with customers, its digital footprint provides source material that makes the organisation a potential target for cybercriminals. Cybercriminals use public information to build profiles of target organisations. This includes published news and reports, internet activity and social media data on suppliers, customers and key people in the organisation.
Why Choose Darkscope
Deep and Dark web monitoring and full social surveillance
Products and service monitory and vulnerability scanning
Full domain and sub-domain monitoring with permutation scanning
SSL & DNS configuration errors and full web service monitoring
Account and High-Risk user monitoring with breach detection
Cyber interferance risk and global cyber threst scoring
Our Awards

Information security excellence award Winner

Hi-Tech innovation award for AI development

Darkscope ranked among the Top 10 Cyber Security Companies
Contact Us

Protecting businesses since 2016 with our award winning AI Powered Cyber intelligence services